RSFirewall! Configuration
The RSFirewall! Configuration panel is composed out of the following elements:
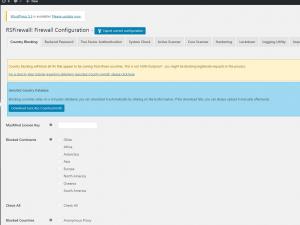
Country Blocking

This is a paid feature.
In order to benefit from this feature please purchase RSFirewall!
- Using this feature you can block all IPs that appear to be coming from specific countries. A country checkbox list will be shown for you to allow/disallow access.
- MaxMind License Key - the country blocking feature will not work unless you install an IP database package; for a step by step tutorial regarding obtaining GeoIP.dat, please click here.
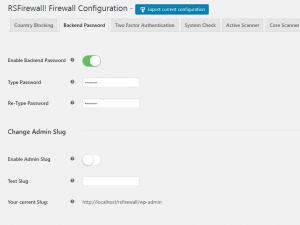
Backend Password
Prevents unwanted access to your WordPress installation by setting up an additional backend password.
- Enable: Yes / No - set to Yes in order to enable this feature
- Type password: Type in the desired password
- Retype password: Retype the desired password for verification
Change Admin Slug
- Enable Admin Slug: Yes / No - Use New Secure Admin URL Slug (ex: myadminlogin)
- Text Slug: Enter the Slug that you want to use!(If the feature is enabled by default the used slug is "login")
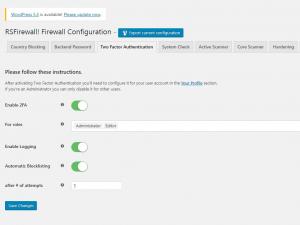
Two Factor Authentication

This is a paid feature.
In order to benefit from this feature please purchase RSFirewall!
- Enable 2FA: Enabling 2FA (Two Factor Authentication) will allow users to select their 2FA method. Compatibility: wp-admin login, WooCommerce, Theme My Login, Ultimate Member, WP-Members, AJAX Login and Registration Modal Popup
- For roles: Specify which roles can use the 2FA system.
- Enable Logging: Enabling logging for the failed attempts.
- Automatic Blocklisting: Enabling Automatic Blocklisting for the failed attempts.
- after # of attempts: This is the minimum number of attempts using the 2FA before the attacker will be added to the blocklist and banned from your website.
After activating Two Factor Authentication you'll need to configure it for your user account in the Your Profile section. If you're an Administrator you can only disable it for other users.
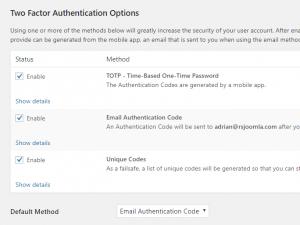
If your user profile is part of the roles selected in the above For roles option a new section will appear on its profile: Two Factor Authentication Options.
Using one or more of the methods below will greatly increase the security of your user account. After enabling at least one method you will be asked for an Authentication Code after you login with your user username and password. The code that you need to provide can be generated from the mobile app, an email that is sent to you when using the email method or an unique code from the pre-generated list. The last two options we recommend to use as backup solutions in case anything happens with your mobile app.
- TOTP - Time-Based One-Time Password: The Authentication Codes are generated by a mobile app (compatible mobile apps: Google Authenticator for Android, Google Authenticator for iOS, FreeOTP or Authy).
- Email Authentication Code: An Authentication Code will be sent to your email address after you login.
- Unique Codes: As a failsafe, a list of unique codes will be generated so that you can still login in case all else fails (you'll need to save these somewhere separately).
After enabling one of these two factor authentication options, you'll need to click the "Update Profile" button to save your settings. You can then click their according "Show details" for more information.
System Check
Here you can find some some configurable options for the System Check:
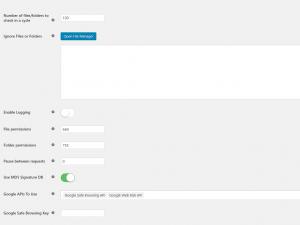
- Number of files/folders to check in a cycle: This is the number of files/folders to check in one cycle. If you set a higher value there's a good chance you will run out of memory and the System Check will not finish. Please use a lower value if you are experiencing issues. The default value is 300.
- Ignore files and folders: During the System Check these folders and/or files will be ignored. Warning! If you select a folder, all its files and subfolders will be ignored as well. Files and folders can be added in the ignore list by clicking on the Open File Manager button which will open a modal in which you can browse through your website's file system.
- Enable Logging: Set to Yes to enable debugging the System Check. The output will be added to WordPress log folder, in the rsfirewall.log file.
- File Permissions: Defaulted to 644 but you can change this value should your server require other permissions. RSFirewall! will check your files for the permissions set here when running the System Check.
- Folder Permissions: Defaulted to 755 but you can change this value should your server require other permissions. RSFirewall! will check your folders for the permissions set here when running the System Check.
- Pause between requests (seconds): you can set up an interval, in seconds, between requests that are sent to the server when the System Check is being performed. This is useful if your hosting provider's server is too sensitive about these requests and regards you as an attacker.
- Use MD5 Signature DB: Yes / No - if this option is enabled, the System Check will take into account an MD5 database to check the PHP files against; please note that this is rather resource intensive.
- Google APIs To Use: choose which Google APIs to use from: Google Safe Browsing API and or Google Web Risk API.
- Google Safe Browsing API Key: RSFirewall! checks your website against Google's constantly updated lists of suspected phishing, malware, and unwanted software pages. Generating this API key can be done as instructed here.
- Google Web Risk API Key: Web Risk is a Google service that enables applications to check URLs against Google's constantly updated lists of suspected phishing, malware, and unwanted software pages. Generating this API key can be done as instructed here.

The above System Check options are paid features.
In order to benefit from these features please purchase RSFirewall!
Active Scanner
Provides a configuration tool for the RSFirewall! Active scanner which actively protects your WordPress website, offering the following configurable options:
- Enable / Disable Active Scanner
- Enable Active Scanner in the administrator(backend) section: this is useful if you don't trust people that have access to your administration.
- Log all blocked attempts: Set to Yes in order to log all blocked attempts. Use this option to identify false alerts on your website. Turn it off once you are done to make sure that automated attempts don't fill up your logs.
- Convert email addresses from plain text to images
- Grab IP from Proxy Headers: some servers are behind a proxy or firewall and will not provide the correct IP. If this is your case, contact the proxy provider and ask them through what header are they sending the real IP. Otherwise just leave these all checked by default and RSFirewall! will attempt to grab the IP by looking through all of them.

This is a paid feature.
In order to benefit from this feature please purchase RSFirewall!
PHP Protections:
- Local file inclusion - disallows directory traversal techniques that might allow an attacker to read sensitive files by exploiting poorly coded extensions.
- Remote file inclusion - disallows attackers to download an run malicious scripts by exploiting poorly coded extensions
- Enable protections for - Form data (POST) enables filtering for information submitted through forms (eg. article editing, user registration etc). While URL data (GET) enables filtering for variables that are located in the URL (eg. http://www.yoursite.com/index.php?option=com_test¶meter1=value1)
SQL Protections:
- Enable protections for - Form data (POST) enables filtering for information submitted through forms (eg. article editing, user registration etc). While URL data (GET) enables filtering for variables that are located in the URL (eg. http://www.yoursite.com/index.php?option=com_test¶meter1=value1)
JS Protections:
- Filter Javascript - by setting this to Yes, the Javascript will be filtered instead of the connection being dropped.
- Enable protections for - Form data (POST) enables filtering for information submitted through forms (eg. article editing, user registration etc). While URL data (GET) enables filtering for variables that are located in the URL (eg. http://www.yoursite.com/index.php?option=com_test¶meter1=value1).
Denial of Service:
- Deny access to the following User Agents: (perl, cURL, Java, Mozilla Impersonators or empty User Agents) The following User Agents are usually automated requests to your website and should not be allowed.
Empty User Agents are usually DoS attack attempts or automated connections to your website.
Perl scripts are used for automated connections to your website.
cURL is used for automated connections to your website.
Java performs automated connections as well.
Mozilla Impersonators are automated scripts trying to impersonate a legitimate browser - Protect forms from abusive IPs - checks if IPs of form submitters exist in the Spamhaus XBL and SBL lists.

This is a paid feature.
In order to benefit from this feature please purchase RSFirewall!
- DNS for resolving lists - Leave this empty to query the lists using one of the public DNS; in some cases, the PBL lists will deny querying using public DNS - if you have your own network DNS, supply the IP here. Multiple IPs can be provided, each on a new line.
- Deny access to the following referers - Referers are visitors coming from another website(domain). You can block multiple domains by specifying them each on a new line. You can also use wildcards, such as *.domain.com which will block any request coming from all subdomains of domain.com(e.g www.domain.com, images.domain.com etc.).

This is a paid feature.
In order to benefit from this feature please purchase RSFirewall!
Automatic Blocklisting:
- Automatic blocklisting: if repeated threats are detected with the same IP address, this will automatically be added to the Blocklist area
- Automatic blocklisting for /administrator login: with this option enabled, failed backend logins will lead to an automatic ban. This option is independent from the CAPTCHA configurable below.
- # of attempts: this is the minimum number of attempts before the attacker will be added to the blocklist and banned from your website.
CAPTCHA:
- Enable CAPTCHA for the admin area: Yes / No This will prompt a CAPTCHA security code in the /wp-admin section. CAPTCHA will always appear unless your IP is safelisted.
- Secret Key
- Site Key
- Activate CAPTCHA after this number of failed login attempts: you will need to specify threshold limit
Backend login:
- Capture backend login attempts: Yes / NoBy enabling this, every time a user fails to login in the /wp-admin section will trigger an event in the Threats.
- Store passwords: Yes / NoSet whether to store the passwords used in the failed login attempts or not.
Uploads:
- Filter uploads by deleting the file(s) instead of the connection being dropped.
- Verify if uploaded files have multiple extensions
- Verify uploaded files for known malware patterns
- Don't upload files with the configured list of banned extensions
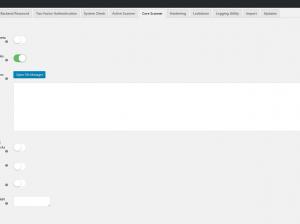
Core scanner:
- Remove the generator meta tag - Removing the generator meta tag from your website's template will protect you from spambots or attackers that target WordPress websites
- Check core WordPress files integrity - Checks a few core WordPress files for integrity, like the WordPress login and index.php
- Monitor the following files for changes - If any of the following files will be changed, you will be alerted by email and an entry will be posted in the System Log.
- Block access to XML-RPC Server (including Pingbacks and Trackbacks) - Stops malicious scripts exploiting the xmlrpc.php and wp-trackback.php files from being accessed (except safelisted IP's).
- Disable REST API - Returns a 404 page when any REST API call is made (except safelisted IP's and the exceptions you enter bellow).
- Allow REST API calls for logged in Users - data-tip="This option allows the logged in Users to use the REST API calls. (Test: http(s)://www.example.com/wp-json/wp/v2/posts/)"
- Exceptions for the REST API - Enter here the exceptions for the REST API. Each on a new line. (Ex: contact-form-7).
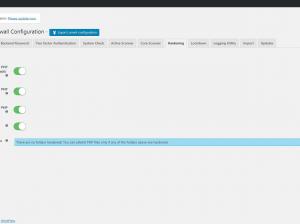
Hardening:
- Stop PHP files in Uploads directory - Stops PHP files from Uploads directory!
Be careful on using this option because many plugins/themes uses PHP files to generate images or save temporary data!
Please use the "Safelist PHP files" option to allow specific files to run properly! - Stop PHP Files in WP-CONTENT directory - Stops PHP files from WP-CONTENT directory!
Be careful on using this option because many plugins/themes uses PHP files to generate images or save temporary data!
Please use the "Safelist PHP files" option to allow specific files to run properly! - Stop PHP Files in WP-INCLUDES directory - Stops PHP files from WP-INCLUDES directory!
Be careful on using this option because many plugins/themes uses PHP files to generate images or save temporary data!
Please use the "Safelist PHP files" option to allow specific files to run properly! - Disable plugin editors - Disables the plugin editors to prevent unwanted core files modifications!
- Remove root readme.html - Removes the root readme.html. The information could be used by malicious users!
- Safelist Blocked PHP Files - After applying hardening to any of the above folders you can safelist any php file located in those folders if you require them to run.

This is a paid feature.
In order to benefit from this feature please purchase RSFirewall!
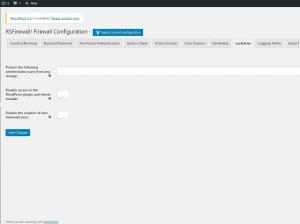
Lockdown:
- Protect users from any changes - this will create a snapshot of the selected users. If any changes will happen to any of them, it will get reverted back immediately. If you want to update your snapshot, you will have to deselect all the users, press Apply and then select the users again and finally Save the configuration.

This is a paid feature.
In order to benefit from this feature please purchase RSFirewall!
- Disable access to the WordPress installer - by setting this to Yes, the WordPress installer will no longer be accessible.
- Disable the creation of new Administrators - by setting this to yes, new users that can login in the /administrator section will be deleted as soon as they are created. Keep in mind that new users (such as the ones added to the Registered user group) will not be affected, unless you are trying to add Super Administrator rights to them (in this case, they will be deleted as well).
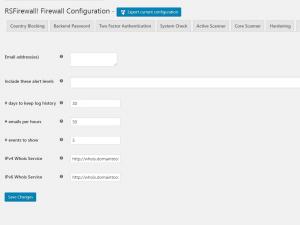
Logging utility
- Logs any events that trigger RSFirewall! so that you can review them. The logging utility also offers the possibility to send out an email if a security event is recorded that has a security level higher then a preconfigured value (low, medium, high, critical).
- To keep the database fresh and prevent if from overloading, a days to keep log history option was added, log entries older then the number of days you set, will be automatically deleted.
- To limit the potential high number of emails (each event / attempt) can potentially generate an email, a maximum number limit of sent emails per hour option has been added. If the limit is reached, no more emails will be generated.
- Here you can also set how many RSFirewall! related events to show in the System Overview by adding a number in the events to show field.
- You can set the preferred WhoIs service for both IPv4 and IPv6. Up until this point, http://whois.domaintools.com/ was used by default. You can use the {ip} placeholder to transmit the IP directly though the URL.
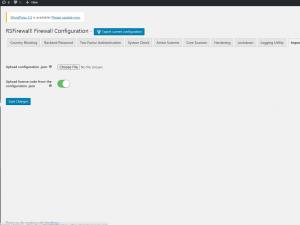
Import
RSFirewall! allows exporting all the configuration settings in order to migrate them on another RSFirewall! installation. The export button is available at the top of the "Firewall Configuration" tab and when is pressed it will generate a configuration.json file which can later be imported using the "Import" tab.
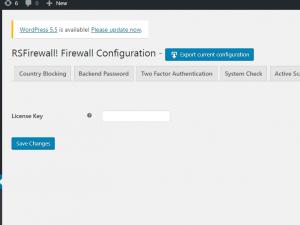
Updates
- Here you need to enter the license code in order to receive update. The license code is generated after you have registered a domain.
- If, for example you have configured RSFirewall! to send email notifications to 3 email addresses, the email counter will be incremented by 3, as each event will generate three emails in this case.
- The more options you have enabled the more protection is offered by the RSFirewall! component however note that these options may affect the overall performance of your site.
One person found this article helpful.